Defense AI Capabilities
Six production-grade AI systems with real code, tests, and verifiable results — engineered for defense security requirements.
TrustShield AI
AI Governance & Trust Scoring Platform
The Problem
Organizations deploying AI systems lack standardized tooling to measure, monitor, and prove trustworthiness — especially for DoD AI ethics requirements and responsible AI mandates.
Our Solution
TrustShield AI provides continuous trust scoring of AI systems with automated bias detection, explainability reporting, and compliance dashboards. Ships with Stripe integration for immediate commercial deployment.
Designed For
- ›AI program offices validating model behavior before deployment
- ›Commanders needing explainability reports for AI-assisted decisions
- ›Compliance teams auditing AI systems against DoD ethical principles
Target buyer: DoD AI Program Offices, CDAO, enterprises deploying AI
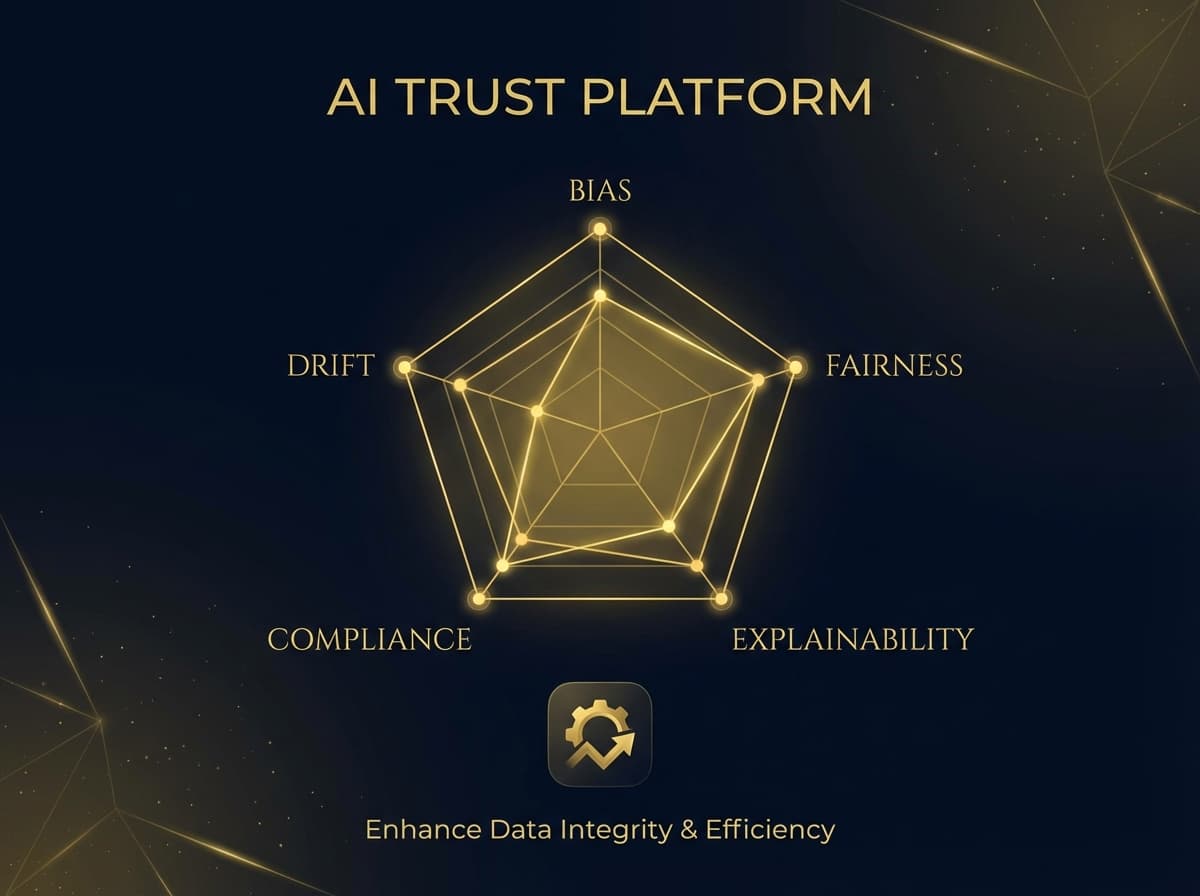
Key Capabilities
- AI trust scoring across 5 dimensions
- Automated bias detection & fairness auditing
- Explainability reports for decision-makers
- DoD AI Ethics Principles compliance tracking
- Model drift detection & performance baselines
- Stripe billing integration for SaaS delivery
Agent Security
AI Agent Threat Detection — 190 Attack Patterns
The Problem
AI agents can be manipulated through prompt injection, tool abuse, and chain-of-thought exploitation. No existing scanner covers the full attack surface of autonomous AI systems.
Our Solution
Agent Security scans AI agent architectures for 190 known attack patterns mapped to OWASP ASI Top 10 and MITRE ATT&CK frameworks. First-mover in the OWASP AI Security Initiative (ASI) space.
Designed For
- ›Security teams scanning AI agent deployments for prompt injection vulnerabilities
- ›Red teams evaluating LLM-powered applications against OWASP Top 10 for LLM
- ›AI program offices validating agent security posture before ATO
Target buyer: AI security teams, red teams, DoD AI programs, CISOs

Key Capabilities
- 190 attack pattern detection rules
- Prompt injection & jailbreak detection
- Tool-use permission boundary scanning
- Data exfiltration pathway analysis
- OWASP Top 10 for LLM coverage
- MITRE ATT&CK mapping for AI threats
ThreatRecon
OSINT Reconnaissance — 15 Scanners, 183 Tests
The Problem
Security teams manually run dozens of separate OSINT tools, then spend hours correlating results. Critical exposures get missed when tools run in isolation.
Our Solution
ThreatRecon orchestrates 15 specialized scanners (DNS, SSL, ports, headers, reputation, breach data) into a single automated pipeline with unified reporting and risk scoring.
Designed For
- ›Red teams conducting automated reconnaissance on target infrastructure
- ›Security assessors generating full OSINT reports for clients
- ›Cyber operations teams monitoring organizational attack surface exposure
Target buyer: Red teams, security assessors, DoD cyber operations

Key Capabilities
- 15 integrated OSINT scanners
- 183 automated test validations
- DNS, SSL, port, and header analysis
- Breach & credential exposure checking
- Reputation scoring across threat feeds
- Automated PDF report generation
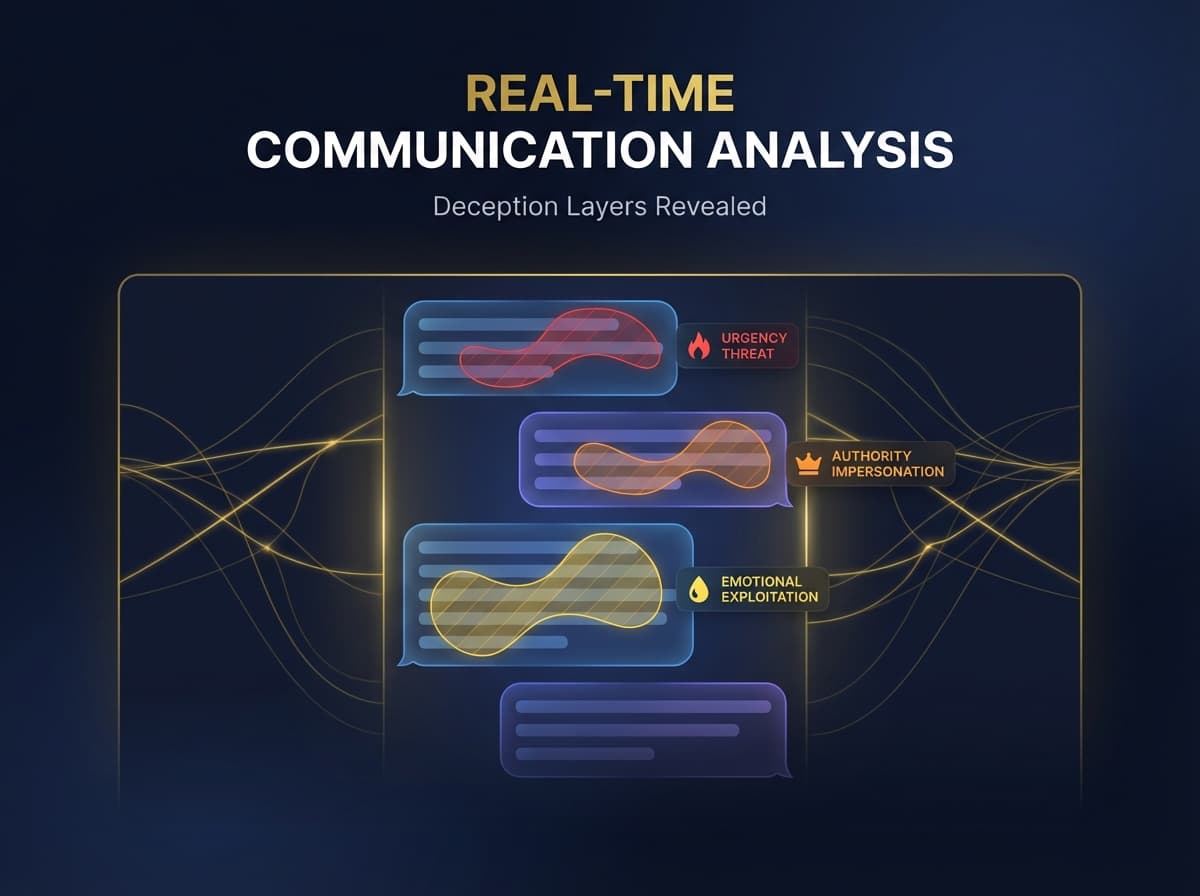
Detection Lab
Behavioral Threat Detection — Live at detectionlab.app
The Problem
CAPTCHAs annoy real users, fingerprinting identifies devices not intent, and bot solver services bypass traditional challenges. Security teams need detection that works without user friction.
Our Solution
Detection Lab scores 22 behavioral signals — motor control, timing patterns, browser artifacts, and content analysis — to detect bots by how they behave, not what they solve.
Designed For
- ›SOC analysts identifying social engineering attempts in communications
- ›Insider threat programs detecting behavioral manipulation patterns
- ›Security awareness teams training staff on adversarial communication techniques
Target buyer: Security awareness teams, SOCs, insider threat programs, developers
Key Capabilities
- 22 behavioral threat signal detection
- Zero-friction invisible bot detection
- REST API with per-signal breakdown
- Stripe billing with tiered API keys
- TENEO auth integration
- Academic foundation (Fitts' Law, sigma-lognormal)
CryptoShield
Modern Cryptography Toolkit — XChaCha20 + Argon2id
The Problem
Defense applications need modern, auditable cryptography but most teams rely on aging OpenSSL wrappers or roll their own crypto — both are risky and hard to audit.
Our Solution
CryptoShield provides a tested, documented cryptography library with XChaCha20-Poly1305 for encryption, Argon2id for key derivation, and Ed25519 for signatures — all algorithms recommended by NIST for post-quantum readiness.
Designed For
- ›Defense developers integrating modern encryption into mission applications
- ›Secure communications teams implementing end-to-end encryption
- ›Compliance teams validating cryptographic implementations against NIST standards
Target buyer: Defense developers, secure comms teams, crypto engineers

Key Capabilities
- XChaCha20-Poly1305 authenticated encryption
- Argon2id memory-hard key derivation
- Ed25519 digital signatures
- Secure key generation & management
- Constant-time comparison operations
- Zero-dependency core library
Red Team
AI Agent Red-Team Testing Framework
The Problem
AI agents need adversarial testing before deployment, but manual red-teaming is slow and inconsistent. Most teams lack the expertise to test AI-specific attack vectors.
Our Solution
Red Team automates adversarial testing of AI agents with scenario generation, boundary probing, and exploitation playbooks. Complements Agent Security by testing the defenses it recommends.
Designed For
- ›T&E organizations validating AI agent security before deployment approval
- ›Red teams generating adversarial test scenarios for autonomous AI systems
- ›Security assessors producing compliance-ready AI safety test reports
Target buyer: AI red teams, security assessors, DoD T&E organizations

Key Capabilities
- Automated adversarial scenario generation
- Prompt injection exploitation testing
- Permission boundary probing
- Multi-turn manipulation sequences
- Integration with Agent Security rules
- Compliance-ready test reports
MITRE ATT&CK Coverage
Threat Intelligence Matrix
ThreatRecon maps to 20 techniques across 5 tactics in the MITRE ATT&CK framework, covering 5 tactical categories.
TA0043
Reconnaissance
6/6T1595
Active Scanning
T1592
Gather Victim Host Info
T1589
Gather Victim Identity Info
T1590
Gather Victim Network Info
T1591
Gather Victim Org Info
T1596
Search Open Technical DBs
TA0042
Resource Development
3/3T1583
Acquire Infrastructure
T1584
Compromise Infrastructure
T1588
Obtain Capabilities
TA0001
Initial Access
3/3T1566
Phishing
T1078
Valid Accounts
T1133
External Remote Services
TA0006
Credential Access
4/4T1110
Brute Force
T1555
Credentials from Stores
T1552
Unsecured Credentials
T1528
Steal App Access Token
TA0009
Collection
4/4T1213
Data from Info Repos
T1114
Email Collection
T1039
Data from Network Drive
T1119
Automated Collection
Platforms & Deployment
Built for Defense Infrastructure
Designed for defense infrastructure and interoperability standards.
Cloud Platforms
AWS GovCloud (US)
Designed for IL4/IL5 deployment profiles
Microsoft Azure Government
Compatible with Azure Gov regions and services
Private Cloud / On-Premise
Air-gapped and on-prem deployment ready
Integration Ready
Palantir Gotham / Foundry
Compatible data integration and object models
Splunk / Elastic SIEM
SARIF output for security event ingestion
ServiceNow
GRC workflow integration ready
Mobile / Edge
ATAK Compatible
Designed for Android Tactical Assault Kit data feeds
Disconnected / DDIL
Architected for denied, degraded, and limited operations
Standards & Formats
SARIF
Static Analysis Results Interchange Format output
CycloneDX SBOM
Software Bill of Materials generation
STIX / TAXII
Threat intelligence sharing compatible
OpenAPI REST
Standard REST APIs for system integration
Need a Custom Solution?
Our platform architecture enables rapid development of custom AI capabilities tailored to your specific mission requirements.
Discuss Your Requirements